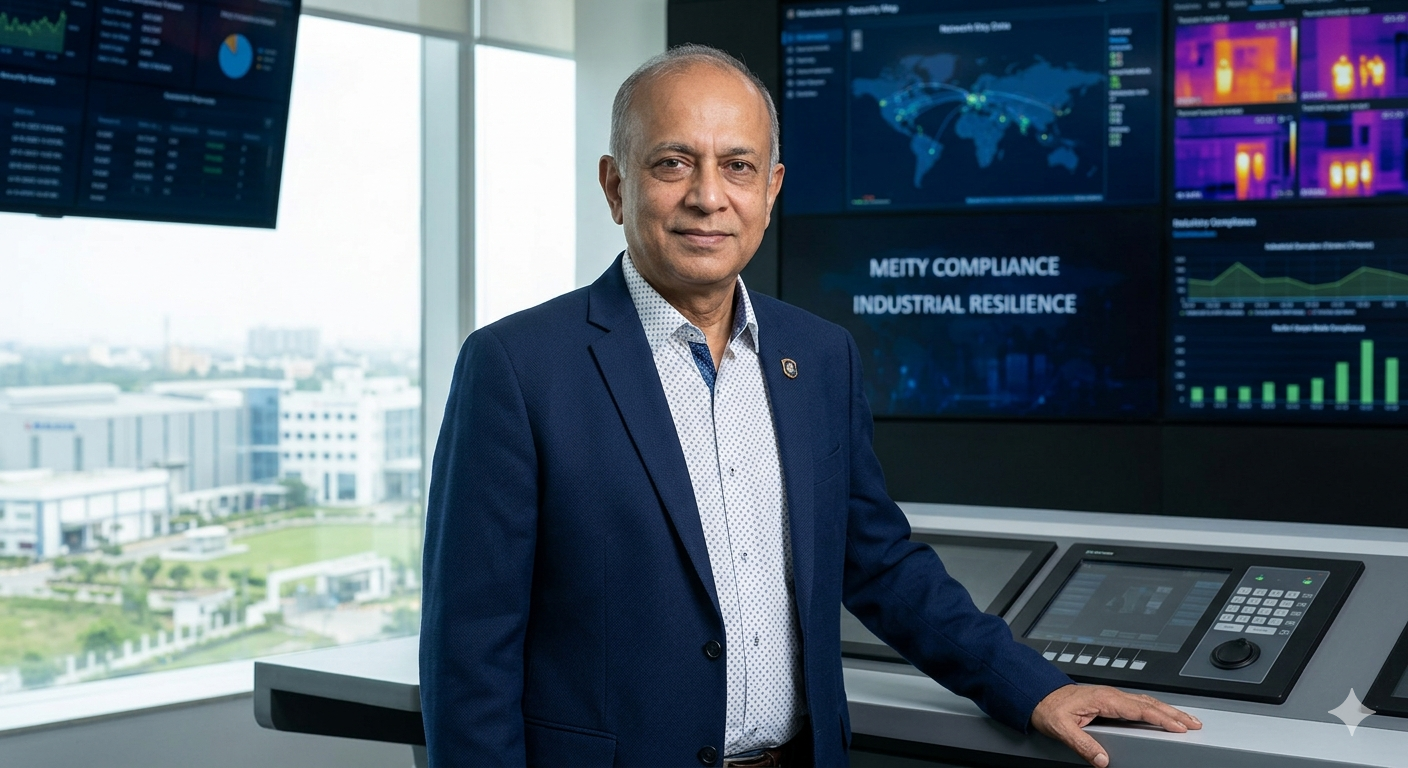
FORTIA engineers the perimeter intelligence layer of modern enterprise security by deploying sophisticated access control and identity management networks. We bridge the gap between physical entry points and digital oversight, ensuring that your mission-critical authorization data flows through a secure, high-fidelity architecture designed for high-stakes security decision-making